How Does Identity Theft Occur?
Thursday, April 22, 2021 8:56 pm, Posted by Absolute Destruction
It would be easier if there were only one way to succumb to identity theft. Unfortunately, there are multiple vectors through which somebody could be the target of a scammer. Data leaks and security breaches can occur on multiple fronts and in different ways. Here are five common ways that identity theft occurs. #1 Stolen […]

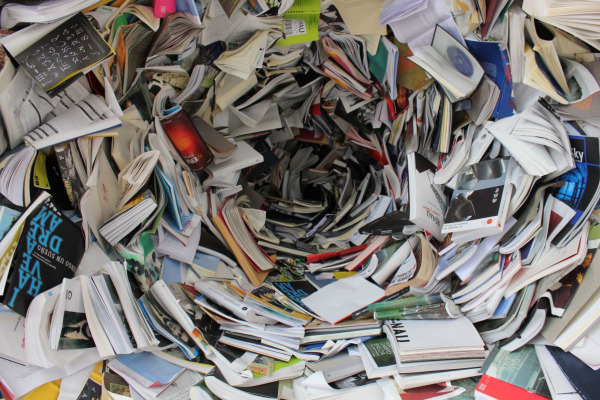
A Guide to Secure Shredding
Thursday, April 15, 2021 7:57 pm, Posted by Absolute Destruction
Everybody knows about the risks of a data breach. Whether it’s multinational corporations or even prominent political parties, we’ve all seen the financial and reputational damage that occur after confidential information leaks. Sometimes it feels like you’re surrounded by people trying to hack your emails and obtain your sensitive information any way they can. Combatting […]
Paper Documentation Matters in a Digital World
Tuesday, February 23, 2021 10:09 pm, Posted by Absolute Destruction
We live in an age of fantastic digital technology, but paper documentation is here to stay. Having a document in tangible form is still the ultimate way to possess it, especially signed contracts or other necessary forms. No matter how digital technology evolves, paper documents will always have a place in your home and office. […]


